Modern antivirus solutions (especially heuristic-based solutions like Sentinel One) are highly complex. They are also paranoid in their efforts to protect your systems from malicious actors. (Rightfully so!)
By their nature, backup agents interact with a system at a low level, using elevated privileges necessary to capture complete data protection. This sometimes causes backup agents to cross paths with antivirus software actively looking to prevent bad things from happening to your system.
Axcient strives to interoperate with all major antivirus vendors, and we perform extensive testing wherever possible. But wild and crazy things still happen from time to time. In the rare event that you need to explicitly exclude your antivirus utility from scanning the x360Recover agent, you may make the following exclusions to your scanning settings.
|
If you have questions about using exclusions with SentinelOne, please review |
Exclude the agent installation folder
The simplest way to exclude the agent from antivirus scanning is to exclude the agent installation folder entirely.
Agent v3
By default, the agent installation folder is C:\Program Files\xcloud
Be aware that this location may have been changed during installation.
HKLM\\SOFTWARE\xCloudAgentService

If you want to make a more targeted exclusion rule, exclude the following files inside the agent installation folder from scanning:
- rsync.exe
- rsync-proxy-client.exe
- xcloud-agent.exe
- xcloud-nas.exe
- xcloud-agent-updater.exe
- xcloud-analysis-tool.exe
- xcloud-endpoint-manager.exe
- xcloud-vss-tool.exe
Agent v2
By default, the agent installation folder is C:\Program Files (x86)\Replibit
Be aware this location may have been changed during installation.
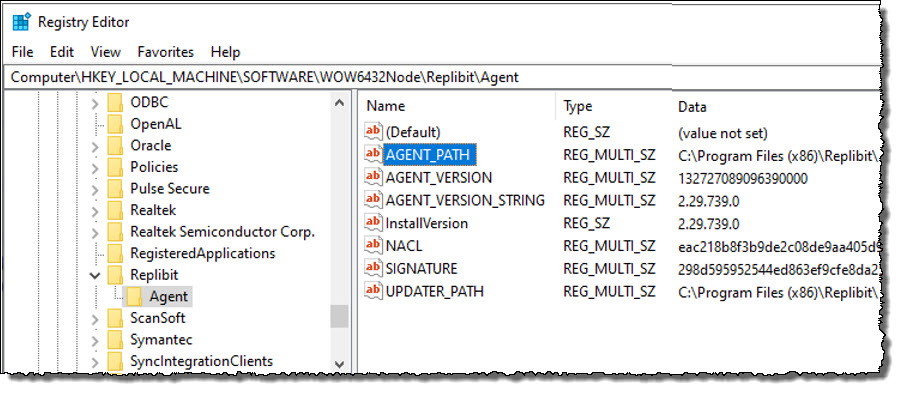
The agent installation path can be found in the Windows Registry at
HKLM\\SOFTWARE\WOW6432Node\Replibit\Agent
 If you wish to make a more targeted exclusion rule, exclude the following files inside the agent installation folder from scanning:
If you wish to make a more targeted exclusion rule, exclude the following files inside the agent installation folder from scanning:
- agentservice.exe
- efsvss-2003-x64.exe
- efsvss-2003-x86.exe
- efsvss-2008-r2-x64.exe
- efsvss-2008-r2-x86.exe
- efsvss-2008-x64.exe
- efsvss-2008-x86.exe
- FastDelta.exe
- frandle.exe
- ManagementService.exe
- uefi-check.exe
- UpdaterService.exe
Exclude the Analysis Tool
You must also exclude the Analysis Tool, which is found at:
C:\Program Files (x86)\Replibit\xcloud-analysis-tool.exe
Exclude AutoVerify / bootVM checks
During the nightly boot check, a communications driver is injected in the system image to create a COM port for communicating between the running VM and the appliance.
On rare occasions, some antivirus scanners block the installation of this driver and prevent Autoverify operations from completing successfully.
To prevent antivirus scanning from interfering with AutoVerify operations, add a scanning exclusion for:
C:\Windows\System32\axcomsvc.exe
Note: This file is not installed into the production environment. It is only deployed temporarily during nightly boot checks within the virtual machine image, and discarded afterward.
SUPPORT | 720-204-4500 | 800-352-0248
- Contact Axcient Support at https://partner.axcient.com/login or call 800-352-0248
- Free certification courses are available in the Axcient x360Portal under Training
- Subscribe to the Axcient Status page for a list of status updates and scheduled maintenance
889 | 1338